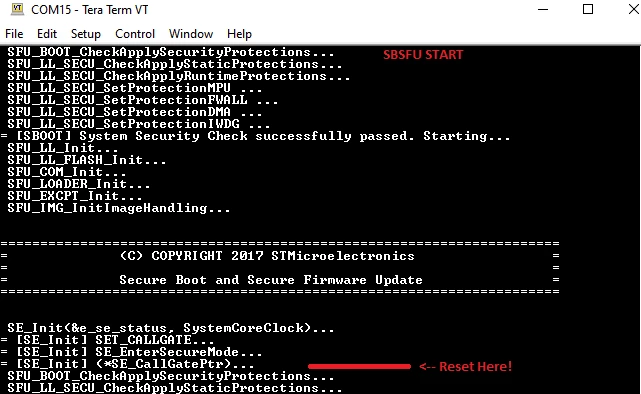
Continuous reset loop with SBSFU on STM32L4R9. Reset always happens right at the moment the secure engine is called.
When the Secure Engine Call (inside SE_Init() function) is called in this line:
e_ret_status = (*SE_CallGatePtr)(SE_INIT_ID, peSE_Status, primask_bit, uSystemCoreClock);
(which is between a SE_EnterSecureMode and SE_ExitSecureMode).
The MCU resets at this point, the reset happens continuously (reset loop) always at this line. The code executed until after SE_EnterSecureMode(&primask_bit); is called. I have added TRACE calls to check this.
Here is the problem area:
/* Enter Secure Mode */
TRACE("\r\n= [SE_Init] SE_EnterSecureMode...");
SE_EnterSecureMode(&primask_bit);
/* Secure Engine Call */
TRACE("\r\n= [SE_Init] (*SE_CallGatePtr)..."); //RESET HAPPENS BELOW:
e_ret_status = (*SE_CallGatePtr)(SE_INIT_ID, peSE_Status, primask_bit, uSystemCoreClock);
TRACE("\r\n= [SE_Init] (*SE_CallGatePtr) done");
/* Exit Secure Mode */
TRACE("\r\n= [SE_Init] SE_ExitSecureMode...");
SE_ExitSecureMode(primask_bit);I have setup all other paramters correctly for STM32L4R9 following AN5056 section 3 (Porting X-CUBE-SBSFU to another board) and have made appropriate memory mapping changes for Secure Engine, SBSFU, Download Area, Active Image defined flash sections. Also the SE RAM1 sections. As per errata, I have defined SE firewall protected RAM1 to be under maximum 128KB (instead of 192KB) - actually just 4KB.
I have also seen this issue and applied the recommendation, to no success:
I have no idea what is happening. I'm not even sure it's the firewall spurious reset. I disabled SFU_FWALL_PROTECT_ENABLE define and the same issue persists. Also if it was an actual firewall (or other reset) I would get the TRACE printout telling me that. This is just a inexplicable reset.
Any help is appreciated. It's a complete showstopper with SBSFU.
