Secure firmware updates from USB Stick on STM32U5 - how to? (2)
Since my previous question on the same topic (see here) I have reviewed probably all the MCUboot/TF-M-based solutions available for ST MCUs. There are currently four options that I am aware of:
- TrustedFirmware-M (TF-M) using the latest MCUboot, implements well-documented PSA-API, actively developed and maintained by community.
Regretfully, this solution appears to be no longer actively supported by ST, STM32U5xx HAL version is 1.0, so no support for new ST MCUs. - ST's TFM, described in AN5447 and UM2851, still available as a part of the STM32Cube_FW_U5_V1.4.0 package under /Projects/B-U585I-IOT02A/Applications/TFM folder, probably abandoned, removed from GitHub for this reason.
- Secure Boot and Secure Firmware Update (SBSFU), described in UM2262 and partially in AN5447, STM32U5G9 supported, based on relatively old TF-M 1.3 (current version is 2.0, version 2.1 to be released in 3 wks).
- X-Cube-Azure example aimed at B-U585I-IOT02A board, no STM32U5G9xx support yet but STM32U5A9xx seems to be handled, based on TF-M 1.3, there are many important updates since then - e.g. MCUboot upgrade to v2.0.0, see release history.
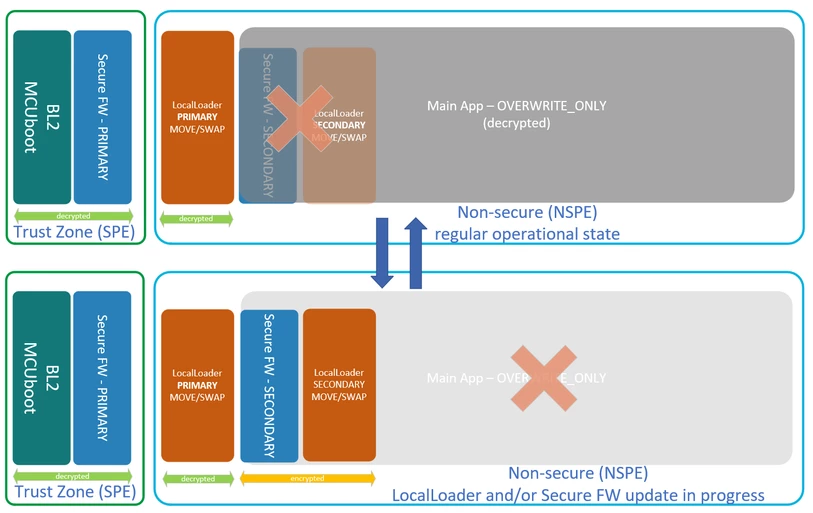
What I need to implement is a very typical real-live scenario - a device (let's imagine it is a fancy coffee machine) based on STM32U5G9 MCU which will be periodically updated by a qualified service technician from USB stick (Y-modem etc. is not considered a modern/convenient hence acceptable solution). Therefore, only the boot loader and the USB Local Loader apps require 100% secure updates (two slots) since any update failure would brick the device. As long as Local Loader is healthy, failure to update the Main App is not a problem, another attempt, e.g. using another USB stick can be easily made.
On the contrary, the Main App, which will be loaded from USB stick by Local Loader and updated the most frequently, does not require primary/secondary slot since the ability to utilize the maximize remaining flash area is way more important.
Needless to say, the Main App image has to be encrypted and signed thus Local Loader needs to be able to verify the signature of the firmware image temporarily placed in SRAM and decrypt it. I do not mind if Secure FW or Local Loader update wipes out the Main App - probably it will have to be updated anyway. Likely Main App image will have to be compressed before it is encrypted and delivered and then decrypted because otherwise it may not fit into available SRAM, unless decryption is done on-the-fly but this is less of the problem.
Conceptually, what I described above is Trusted Client scenario, defined in PSA-API, section 3.3.3.
I am afraid that only the first solution listed above (TrustedFirmware-M) guarantees that recent fixes and security updates can be quickly applied. The only downside is that probably I will have to update HAL to a recent version myself and maintain it. I already know it is not a simple task since among STM32U5xx MCUs only STM32U585 is supported and many things are hardcoded.
- Is it possible to implement the above-described scenario with SBSFU? Although SBSFU does not incorporate the latest TF-M and MCUboot versions, it may be the quickest way forward since SBSFU receives current ST updates the most frequently.
- Is there any chance SBSFU will be updated to a new TF-M version soon or ST will truly support current TrustedFirmware-M (TF-M) solution? It seems that today the choice is between either new MCUs and old TF-M or new TF-M but no recent MCUs.
Please comment/advise.