STM32U585: AES GCM Tag mismatch
Good afternoon,
we are facing issue with AES GCM Tag generated with STM32U585.
In particular we compare the results generated by the microcontroller with the ones generated by an application developed with C#.
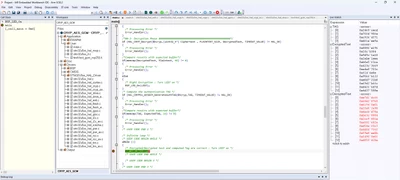
This is the code running on the microcontroller
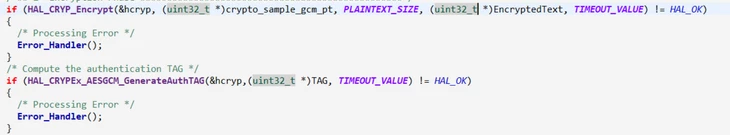
Key size is 256 Bit set to all 0 just to speed operations. Tag size is 128 bit. I know that the IV vector must have the last byte set as 2 an I dit it as requested.
uint32_t pKeyAES[8] = {0x00000000,0x00000000,0x00000000,0x00000000,0x00000000,0x00000000,0x00000000,0x00000000};
uint32_t pInitVectAES[4] = {0x00000000,0x00000000,0x00000000,0x00000002};
__ALIGN_BEGIN static const uint32_t HeaderAES[4] __ALIGN_END = {
0x24825602,0xbd12a984,0xe0092d3e,0x448eda5f};
Plaintext is a simple 48 bytes buffer (so a multiple of 16).
The EncryptedText is identical to the one generated by the application: good.
On the other hand the generated Tag is always different....maybe we are doing something wrong....could you help us with this topic?
Thanks
Best regards