Using derived hardware key (DHUK) with AES on stm32u5
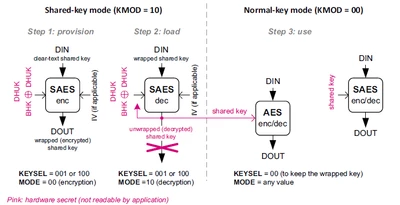
I've been trying to set up the AES peripheral so that it's only using the hardware derived key from the SAES peripheral (without setting any clear text key). However, the only method mentioned in the reference manual on using the DHUK is through the shared-key mode, where a clear text key is encrypted and passed on to AES.
I would like to know if there is a way to use AES with no clear text key (key is entirely hardware generated).
Any insights or alternative approaches would be greatly appreciated.
