Solved
Unable to write Password for AREA1 on a fresh ST25TV02KC Tag using RFAL
Hello ST Community,
I am encountering a persistent issue while attempting to program a new password for the user memory in AREA1 of an ST25TVxxXC NFC tag using an ST25R200 reader and the RFAL library.
I have followed below procedures for setting the password:
- Get a 2-byte Random Number from the tag using rfalST25xVPollerGetRandomNumber() api.
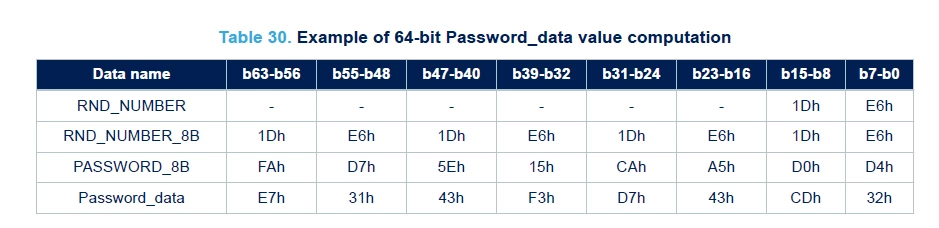
- XOR the desired 64-bit password with the obtained Random Number, as per table 30 of ST25TV02KC datasheet
- Use the PresentPassword command to enter secure session mode with default password {0,0,0,0,0,0,0,0} using rfalST25xVPollerPresentPassword() api.
- Use the WritePassword command to set the new password using rfalST25xVPollerWritePassword() api.
I have written a local function to perform XOR operation and confirmed that the XORed output matches as per below table of ST25TV02KC datasheet:
Below is the code snippet for the same:
platformLog("\r\nUSE CASE : Writing password.\r\n");
uint8_t rnd_num[ 1 + 2 + RFAL_CRC_LEN ]; /* Response Flags + RND_NUMBER(2) + CRC */
/* Read UTC_EN from System Configuration Register @(FID=02h, PID=00h) */
err = rfalST25xVPollerGetRandomNumber(reqFlag, uid, rnd_num, sizeof(rnd_num), &rcvLen);
platformLog("Received Random Number : %s %s\r\n", (err != RFAL_ERR_NONE) ? "FAIL" : "OK Data:", (err != RFAL_ERR_NONE) ? "" : hex2Str( &rnd_num[1], rcvLen - 1));
uint8_t default_pwd[8] = {0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0}; //64-Bit password
uint8_t pwd[8] = {0x11, 0x22, 0x33, 0x44, 0x55, 0x66, 0x77, 0x88}; //64-Bit password
uint8_t coded_pwd[8];
uint16_t xor_val = (rnd_num[1] << | rnd_num[2];
/* 2.Make the password and Random Number XOR. */
get_xored_pwd(pwd, PWD_64_BIT, xor_val, coded_pwd);
platformLog("Raw Password : %s %s\r\n", (err != RFAL_ERR_NONE) ? "FAIL" : "OK Data:", (err != RFAL_ERR_NONE) ? "" : hex2Str( &pwd[0], 8));
platformLog("Coded Password : %s %s\r\n", (err != RFAL_ERR_NONE) ? "FAIL" : "OK Data:", (err != RFAL_ERR_NONE) ? "" : hex2Str( &coded_pwd[0], 8));
/* 3.Use the Present Password function to enter secure session mode. */
err = rfalST25xVPollerPresentPassword( reqFlag, uid, 0x01, default_pwd, 8);
platformLog("Opening Secured Session : %s (Error Code: %d)\r\n", (err != RFAL_ERR_NONE) ? "FAIL" : "OK Data:", err);
/* 4.Start writing the password that you want */
err = rfalST25xVPollerWritePassword( reqFlag, uid, 0x01, coded_pwd, 8);
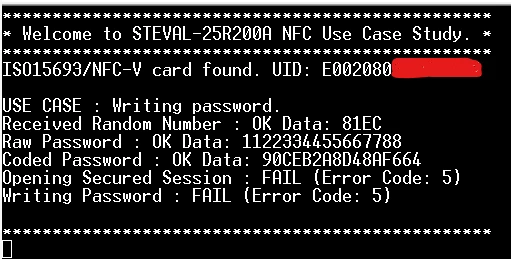
platformLog("Writing Password : %s (Error Code: %d) %s\r\n", (err != RFAL_ERR_NONE) ? "FAIL" : "OK Data:", err, (err != RFAL_ERR_NONE) ? "" : hex2Str( &coded_pwd[0], 8));However, I am unable to successfully enter the secure session using present password api, consistently receiving RFAL_ERR_REQUEST (invalid request or requested function can't be executed at the moment).
Below is the debug prints on Tera Term terminal:
Any guidance, insights into common pitfalls, or suggestions for further debugging would be greatly appreciated.
Thank you for your time and assistance.
Regards,
Tanuj
