STM32U585 - TFM Application HKDF Implementation Using PSA Crypto
Hello
I am taking the reference implementation of the HKDF Algorithm using PSA API in the TFM Application Project and using the following algorithm :
PSA_ALG_HKDF(PSA_ALG_SHA_256);
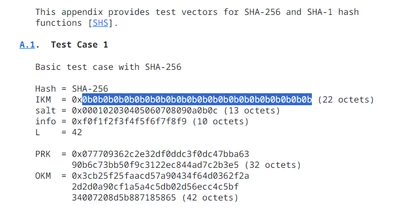
I m able to export the output key to the console and am getting an output for the test vectors taken from RFC5869 as shown below:
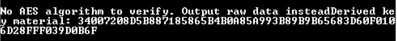
But when using the same Hash, IKM, Salt, Info as given in the test vector set Im getting a different value as shown in the below format:(value displayed Derived Key Material is expected to be same as OKM in above Figure)
The codes i have used the same format that was already present to be specific:
TFM_Appli_NonSecure->Middlewares/trustedfirmware/test/crypto_tests_common.c :
struct test_result_t *ret);
Requesting your support to solve this issue and validate the HKDF Function Implementation
Thanks and Regards
Philip Jose
