How to select format type and KeySize in STM32 Trusted Package Creator?
I am following the "How to deploy SSP using a step-by-step approach". I am working on "3.1.2.2. Secret file content for STM32MP2 series". The target MPU is STM32MP257F. I have some questions as below:
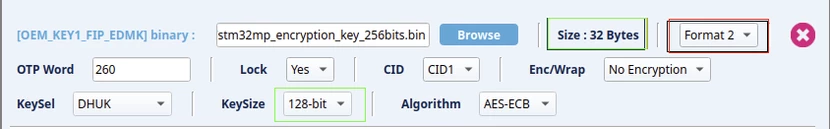
1. How do I know whether to choose "Format 1" or "Format 2"?
2. I selected the binary file as FIP-EDMK, which is 256-bit but the KeySize shows 128-bit and it won't let me select 256-bit again. Is this acceptable?