Associate III
July 10, 2025
Solved
Review a secret file content for STM32MP2 series to enable secure boot
- July 10, 2025
- 1 reply
- 521 views
My goal is to create a SSP payload and write it to the OTP of the STM32MP257F chip. The OS running on my KIT is based on OpenSTLinux.
To get the SSP Payload, a Secret file is required. I just need secure boot.
I refer to the following sources:
- How to perform Secure Boot from Distribution Package
- How to deploy SSP using a step-by-step approach
- What is the meaning of Enc/Wrap when create a secret package?
- How to select format type and KeySize in STM32 Trusted Package Creator?
The contents of my Secret file will include the components as shown below. (Json file attached)
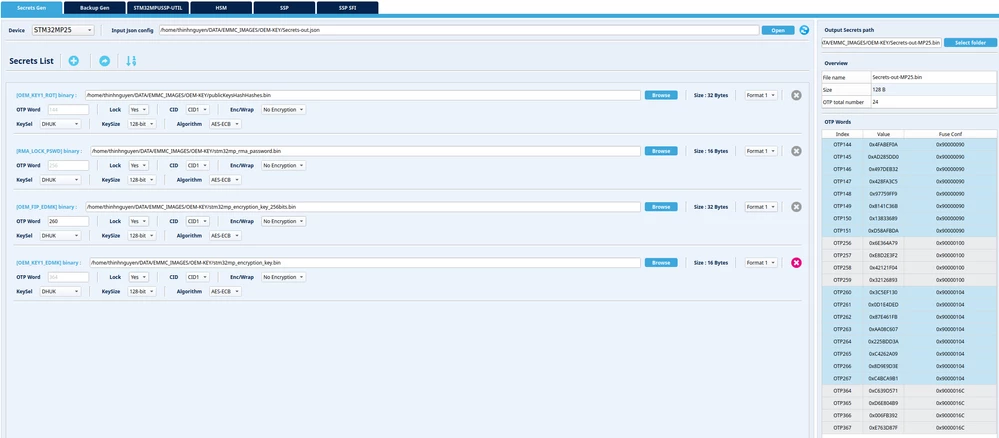
Is a secret file with such components enough for secure boot? And please advise if there are any invalid options in the Secret list
