Hello,
Understanding 2 is correct.
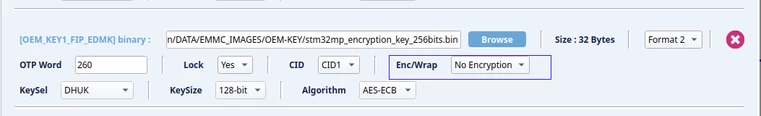
More precisely, the FIP-EDMK will be Encrypted of Wrapped by the embedded SSP software during the SSP procedure.
Enc/Wrap feature is used to obfuscate the secret programmed on the SoC :
- No Encryption : the FIP-EDMK is programmed as is in the OTP. If you dump the OTP you will read the same value as the input file.
- Encryption : the FIP-EDMK is encrypted then the encrypted data is stored in the OTP. If you dump the OTP the data is different from the input file. Any input file that is a multiple of an AES block can be encrypted.
- Wrapping : This a special feature of SAES. The FIP-EDMK is processed by SAES (step 1 figure 538 of @Zakaria1 screenshot). Then the wrapped key is stored in the OTP. If you dump the OTP the data is different from input file. Wrapping can only be used to obfuscate encryption keys.
The main advantage of Wrapping against Encryption is that when you unwrap the FIP-EDMK to retrieve the value the input file, SAES directly write the FIP-EDMK in the key register of SAES : step 2 figure 538 of @Zakaria1 screenshot. So the FIP-EDMK unwrapped is never accessible by the OEM firmware deployed on the product (CubeHAL, OpenSTLinux, ...). The OEM firmware is using the FIP-EDMK without having access to its real value, hence it limits the risk of leak of the FIP-EDMK.
Note : In OSTL, TF-A does not support unwrapping the FIP-EDMK. So if you want to execute a secure boot with an encrypted FIP, you should select "No Encryption" in STM32 Trusted Package Creator.